Every CVE remediated in your private cloud infrastructure. SoftIron becomes a CNA. The virtuous circle of transparency and security in HyperCloud.
Today we announced that SoftIron is now authorised by the Common Vulnerability and Exposures (CVE®) Program as a CVE Numbering Authority (CNA). I wanted to take a little time to explain why this is important and, more broadly, the approach that we take to handling vulnerabilities that we find when it comes to HyperCloud.
First, let me give a little background on the CVE Program for those not familiar with it.
The CVE Program, CVEs and CNAs
Almost 25 years old at this point, the CVE Program was launched in 1999. Having grown over the years it has also spawned many subsequent initiatives and programs, including NIST’s National Vulnerability Database and is now sponsored by the Cybersecurity and Infrastructure Security Agency (CISA), of the U.S. Department of Homeland Security (DHS).
It seeks to provide a common framework to identify, define and catalogue publicly disclosed cyber security vulnerabilities. As each vulnerability is detected, reported, and assessed, a CVE record is created and a CVE ID is assigned. This helps stakeholders, in reality, anyone developing or using technology hardware or software, to keep track of and/or collaborate on each vulnerability, responding to the severity of the vulnerability as required. These IDs are assigned by a network of numbering authorities (CNAs) and are now the de facto standard worldwide for tracking vulnerabilities.
From today, SoftIron joins the group of leading IT vendors, research organisations, CERTS and others to become a CNA in their own right, able to assign CVE IDs to vulnerabilities and publish CVE Records within their own specific scope of coverage. For SoftIron our scope covers any vulnerability we identify associated with HyperCloud.
Identifying those “needles in the haystack”
Software today is rarely written completely from scratch. Libraries large and small, of both proprietary and open-source code are used to add various bits of functionality to more complex software when there is little or no value in uniquely replicating it.
And whether or not part of one of those libraries, vulnerabilities in software do, of course, occur giving hackers the opportunity to compromise the software, the device or devices running that code, and/or the data that is stored or is in transit through it. With such a complex web of authorship and ownership of the code it’s important that when these vulnerabilities are identified, both the owners of that code and anyone using it are notified as quickly as possible, with as much information as possible, so that remediation can occur.
Managing vulnerabilities in the wild
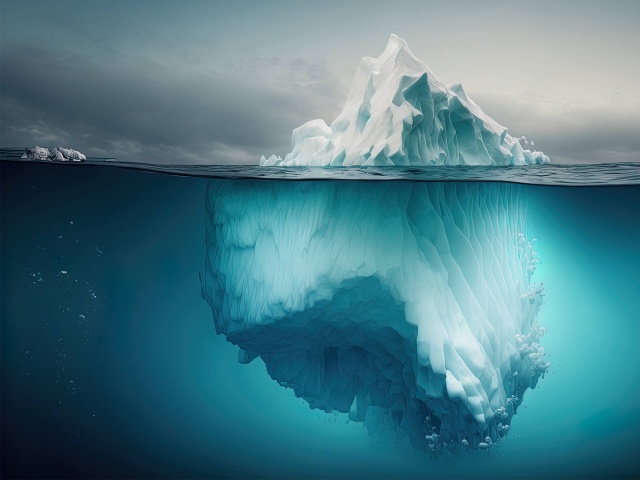
It’s not hard to imagine the challenge of managing this across a broad real estate of multi-vendor, multi-product, data centre infrastructure as an IT team.
Just think of all of the brands and individual product lines of hardware with all the versions of firmware they might be running. Think of the operating systems, both proprietary and open source that are deployed as well as all the application software that could be running at any moment in your data centre. Think of the complex network (and often quite easy to unintentionally disrupt) that interconnects all of this equipment – both at a hardware and software defined layer. Imagine now trying to both track the vulnerabilities that you may be exposed to by operating all of that and then trying to make a meaningful plan to address or remediate against the vulnerability or vulnerabilities identified. And remember, you’ll need to be confident that your plan can be executed with no planned or unplanned service downtime so understanding the interdependencies between all of that kit will be important too.
The HyperCloud advantage in addressing CVEs
HyperCloud is a new class of product. A new way to build infrastructure, designed and manufactured in a new way to achieve that. Everything that is required for you to build and operate your own private cloud is contained within HyperCloud and is supported by SoftIron.
When you build from component and source code level up, as we do, a complete platform the benefits that can be gained are many and various. In some respects, it’s remarkable so few take this route, instead relying on a software veneer for differentiation (but that’s a story for another post). And if you’ve been following the SoftIron journey for any length of time you’ll know that one of those benefits is what we call Secure Provenance – access for those for whom security is absolutely paramount, to audit our entire product realisation process. This, we believe, is unique in our industry. The ability to review every line of code, every component, every design, our manufacturing facility and process, all for themselves, enabling them to build out the most accurate risk mitigation strategy possible and apply the best-matched security controls.
While it’s a big offer on our part, for most enterprise or public sector type organisations the “lift” required to take that on – to acquire and/or build the skills needed and take on a regular audit of this calibre, is too great to justify the return on investment. And that’s fine, but there are still a multitude of other security benefits that every customer receives from our approach.
Handling CVEs is one more of them.
With our complete visibility of every line of code we ship within the platform, we can both identify and remediate any and every CVE in any of the libraries of code we may use to build from. In fact, that’s exactly what we do. We constantly monitor the CVE registry, and at every release of HyperCloud software, we ensure that we have remediated every known vulnerability within HyperCloud before shipping.
At every release, your entire HyperCloud-based private cloud infrastructure, not just portions of it, has no known vulnerabilities. We believe there is no other vendor, and no other product platform able to claim this. It’s transformational for security professionals.
Becoming a CNA ourselves now also means that we can immediately notify the public at large of any vulnerabilities we identify, whether within our own code or in other products and software we use.
For HyperCloud users, upgrading their entire private cloud requires the application of a single patch, ensuring every part of your private cloud is completely up to date and vulnerabilities are remediated.
In the same way your public cloud provider removes the headache of worrying about vulnerabilities in the infrastructure, SoftIron and HyperCloud do the same for your private cloud.
To find out more contact us and arrange a chat.