If you’ve been following SoftIron for a while it won’t have escaped your notice that unusually (almost uniquely) in the IT industry, we design and manufacture our own appliances from the component level up, rather than relying on an often limited selection of “off the shelf” designs and sub-assemblies that are manufactured by one of the big sub-contractors.
One such “standard” sub assembly is the Baseboard Management Controller (BMC).
The BMC is a small but critical part of the hardware’s design. It is the first set of electronics to receive power on bootup and from there on in its role is to monitor the physical state of health of the appliance as well as manage power cycles and reboots as necessary. It also serves as a remote management interface of last resort for remote hardware interaction, tending to have a separate network connection from the rest of the production network. Without it, lights-out data center operations would be nearly impossible.
As the design of servers has been commoditized, so the design of the BMC – chip, board and related firmware, has also become commoditized, to a point where today there are less than a handful of options to choose from available in the “off the shelf” market.
Lack of choice a good thing?
If your glass is half full, you might argue that a lack of choice has actually led to de facto standardization. If the BMC is the same through multiple manufacturer’s servers then, as a sysadmin, life is made simpler if I want to try to automate tasks across my IT real estate. Indeed, some of our largest customers have told us that they even specify what BMC must be used in any server procured in order to achieve this. There’s no doubt, in farms of generic servers, this approach has benefits. But there’s a cost…
The cost of “lowest common denominator” approach
While there are clearly benefits for the Sysadmin, it’s not all upside. There are two key downsides to this approach.
1. Hardware compromise
The first to consider is the security risk that the compromise of the BMC may create. Remember the BMC is the first set of electronics to receive power in the hardware design. By its nature it has full control of the hardware before the OS or any other software for that matter can boot. If you “own” the device’s BMC, you own the device.
Security hacks are all about risk and effort vs. reward. Hardware hacks are hard to achieve as you need physical access to the hardware at some point in its life (whether in the supply chain or after deployment), but the payoff can be huge – super hard to detect once installed, fabulous access to low level data and/or control over hardware (think critical national infrastructure, for example, where simply powering down the device might be all that’s need to create havoc).
If there are only a couple of designs in use across a vast swathe of IT infrastructure, then the payoff of compromising one of them is potentially enormous. Indeed, injected into the supply chain early enough and the degree of the potential effect of such a compromise is almost incalculable. The BMC is a prime target.
2. “Task specific” management
So there’s a security risk. There’s also a downside in the generic nature of that design. If the BMC could end up in all sorts of compute, network and storage devices, by its nature then the capabilities it can undertake must in turn be reasonably generic. In a software defined world where the “hardware doesn’t matter” then maybe that’s an OK trade-off, but if you are striving to optimize your infrastructure – to deliver new benchmarks in performance, efficiency and control then this is a huge missed opportunity.
As customers increasingly look to larger scale deployments of edge infrastructure we think this can only become a bigger issue. In a data center in a place where a data center didn’t used to be, and without intelligent hands close by to cosset the deployment the more comprehensive the degree of low level control we can exert over the hardware the better in solving real world admin and control issues.
The SoftIron BMC
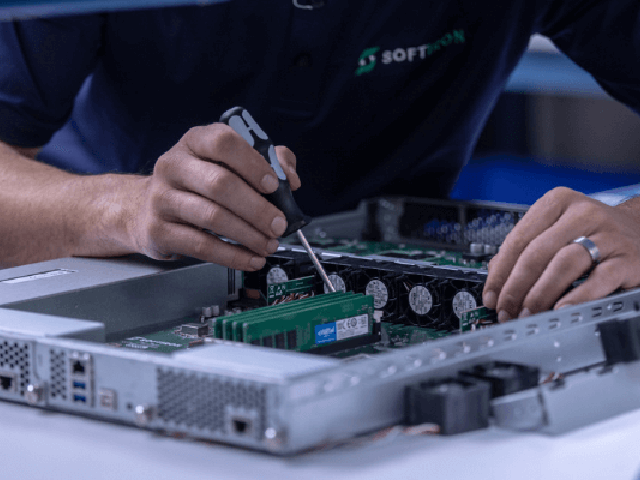
The SoftIron BMC ensures we have complete control over our own appliances. We populate the boards on our own assembly line giving us total control of the manufacturing process, start to finish. We write our own BMC software and compile it from source code, giving unrivaled transparency into this critical sub assembly of the finished product. Ask your existing vendor what’s in the code running on the BMC, or indeed where and how the BMC was made and from what, and see what they say(!)
For our customers that care about secure provenance, a common BMC across all of our products also reduces the complexity of their audit, enabling them to review this sub assembly design once regardless of the number of SoftIron products they deploy.
Having our own BMC design not only pays dividends in terms of secure provenance, but also gives us the ability to continue to innovate in the ways in which we can add value for customers in enhancing what we call ”fleet management” – helping solve and ease real world issues in managing a fleet of data center infrastructure remotely with only relatively unskilled support to hand.
Over time you’ll see us release a number of capabilities made possible by “owning” the BMC design across the range of SoftIron products. For now though, you’ll just have to let your imagination run wild.
For those used to deployment using a generic BMC design, we realise that this may require a change in the way you define your hardware requirements in the future.
We think it will be worth it.